Emulyator Usb Klyucha Dlya Cnckad

May 9, 2010 - This is only a memory dump file, to make an emulator you need Dump + Q/A (maybe from USBtrace or bushound) Also you should know that. Mysql recovery toolbox zip registration key west.
When buying a licensed computer program a user gets specified number of its working copies (in most cases only one). Accounting software source code c. Naturally, the term 'copy protection', which is generally accepted in the international practice, is rather conditional, as it is almost always possible to rewrite the information from the medium and make its multiple backup copies. The matter, however, is that to protect copyright and the commercial rights of developers, the program must be executed only on a limited number of computers, which is usually defined in a user agreement. In this regard, the main mission of software copy protection is to guarantee the impossibility of running a licensed program on more computers than allowed by its developers and distributors.
To protect their solutions against illegal copying and unauthorized execution, software providers use special hardware keys that lock and unlock programs so that they cannot be accessed without the permission of the developer or the distributor company. In this article, we’ll highlight the pros and cons of hardware security keys and tell you about the most efficient dongle key emulator that will let you access your hardware solutions remotely. Contents • • • • What’s a dongle key?
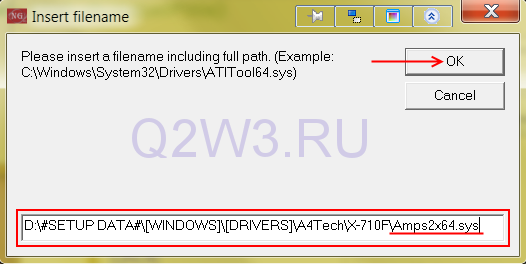
A hardware key (also called a 'dongle') is a small electronic device that plugs into the USB port of the computer. Once the protected program is launched, it starts looking for the key and its parameters. If the security key is not found (the devices usually generate a response code which is analyzed by the app), the program will not run (or access to the data will not be allowed). The sphere of application of security keys has significantly expanded in recent years. Today, dongles serve for identifying the software copy owner, storing their personal electronic signature or confidential information, can be used as a credit smart card or electronic money. Benefits and drawbacks of hardware dongle protection Pros: • You can insert your USB dongle into any computer on which you need to run the program; • The hardware solution does not require a drive; • An electronic key is able to perform cryptographic transformations; • Modern USB keys can execute arbitrary code written by the developer (e.g. Guardant Code, Senselock, etc.) Hardware keys ensure reliable protection of a software copy thanks to the mechanism which does not allow the key security information (cryptographic keys, downloadable codes) to leave the device while you access it.
Unchecky is a small and lightweight application that has been designed to keep potentially unwanted programs off your computer by keeping your checkboxes clear during file installations. The application works by automatically unchecking unrelated offers during the installation process. This in turn saves time and effort in clicks and it makes it less likely to miss a checkbox of an unwanted offer or potentially unwanted program (pup). Overall, Unchecky is a small and lightweight application that runs silently in the background of your computer. It uses only a small amount of system resources and can potentially protect your system against installing unsolicited browsers or applications that you didn't intend to install.